How to respond to a Business Email Compromise - Part 1
The growing adoption
of cloud services is rapidly occurring, as many businesses move their critical
information and infrastructure from local managed environments to the cloud.
However, threat actors are also pivoting their operations to target cloud
environments at an equally rapid rate. In this new era, cooperation and trust between
incident response specialists, businesses, and law enforcement is needed to
disrupt these threat actors. The majority of cyber incidents we respond to are
cloud-based business email applications. In these types of incidents, a threat
actor gains access to a user’s email and often steals money or data. Apart from
any direct financial losses or un-authorized access of sensitive data, these
incidents can also disrupt business operations related to its cloud systems
that are relied on every day. This problem is further complicated because
critical information required to investigate cloud-based business email
applications are often not available or the knowledge needed for a forensic
examination is not completely understood. Therefore, in this blog series, we
will share our knowledge, tooling and experiences of these types of incidents,
which can help disrupt these threat actors and contribute to building trust in
society. We hope other organizations in this field will follow this approach
and share their knowledge in order for everyone to be able to tackle these
incidents and help those in need of assistance.
What is a BEC?
BEC is a type of attack often targeting a company’s executives or employees in accounts payable; with the intent of tricking a victim into transferring money to fraudulent accounts. The US Federal Bureau of Investigation estimates that approximately $12.5 billion dollars was lost to BEC attacks from October 2013 to May 2018. Losses from a single attack can range from several thousand to several million dollars – with at least one victim losing approximately $21 million. BEC attacks often employ two techniques to trick their victims, which include spoofing a company and/or its trusted partner’s domain, or using an employee’s display name in the header of the email. The goal of the threat actor is to evoke a sense of legitimacy and trick high-level executives or employees in accounts payable to initiate the transfer of funds. BEC schemes predominantly use existing business productivity software to achieve this objective. The most widely used business productivity tools are provided by Microsoft but Google continues to strive for a larger market share. The greater utilization of Microsoft business products, creates a larger attack surface for BEC attacks to occur. According to cyber security company Agari(PDF), phishing attacks impersonating Microsoft occur 70 percent of the time and 45 percent of all major secure email gateways being targeted in BEC attacks are Microsoft. These figures coincide with Microsoft’s large market presence but also indicate a need for specialized tools and solutions to help prevent, respond, and mitigate attacks targeting Office 365 environments.Challenges
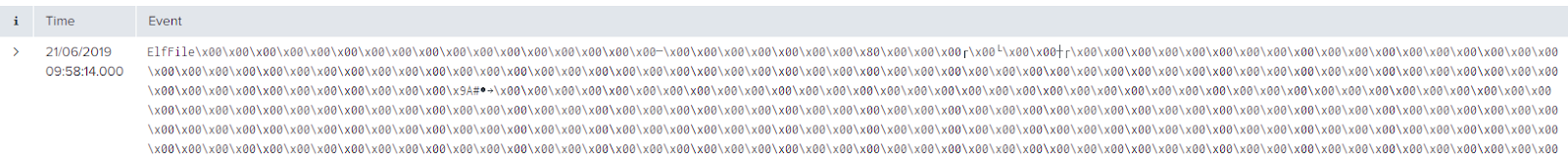
The challenges faced in our initial investigations of BEC cases were greatly exacerbated by the lack of technical information and tooling available. So through trial and error, we developed the necessary knowledge base and tooling to help our customers investigate BEC attacks against their businesses. We recently investigated several cases that caused significant losses to our clients. In one case, a firm incurred substantial monetary losses of more than €100,000. While in another case, several thousand highly confidential emails were forwarded to an unauthorized user, which extended beyond financial losses into significant legal implications. Based on these incidents, we identified several re-occurring challenges.Two primary challenges identified are log acquisition and log analysis. Log acquisition from an Office 365 environment is particularly challenging because of the sheer amount of logs stored and their export limits. This notion further complicates analysis of those logs. However, with the rise of BEC cases, Microsoft has taken some steps to improve detection and analysis capabilities for its Office 365 environment but with several major caveats.
One improvement observed is the auditing of a user or administrator’s activity, which is turned on by default and captured in the audit log. Furthermore, an organization can enable a default policy that triggers an alert when a forwarding or redirect rule is configured. However, in a number of cases we have investigated, alerts are sometimes not configured correctly, which causes the wrong people to receive the alerts or simply creates an overflow of alerts – leading to alert fatigue. We have also observed cases where millions of events are stored in the audit logs for a period of weeks. This raises the question, “what is worth your time to analyze?”
The Solution
The aforementioned challenges have inspired us to think of a solution for log retention and for detection of a BEC attack. In the second blog post, we will go into detail on how to acquire the Office 365 Unified Audit Log using a PowerShell script. In the third blog post, we will outline the process of detecting malicious or suspicious behavior in the Office 365 Unified Audit Log.


Comments
Post a Comment